Penetration test home user
 For those of us who can remember, something called a personnel department was the go-to place to apply for a job, fill out Breach, rinse, repeat - when will companies get the IT security basics right? You can use these tags: June 28, at 8: It renders itself useful for web applications, wireless systems, networks etc. No, create an account now. Anyway, what do you expect to prove by this?
For those of us who can remember, something called a personnel department was the go-to place to apply for a job, fill out Breach, rinse, repeat - when will companies get the IT security basics right? You can use these tags: June 28, at 8: It renders itself useful for web applications, wireless systems, networks etc. No, create an account now. Anyway, what do you expect to prove by this?

Agnes. Age: 25. iґm a real pleasure for every gentleman who is looking for a great private time full of passion ..... Iґm full of humour and easy talk to, with my warmth and passion i will captivate you and please you.

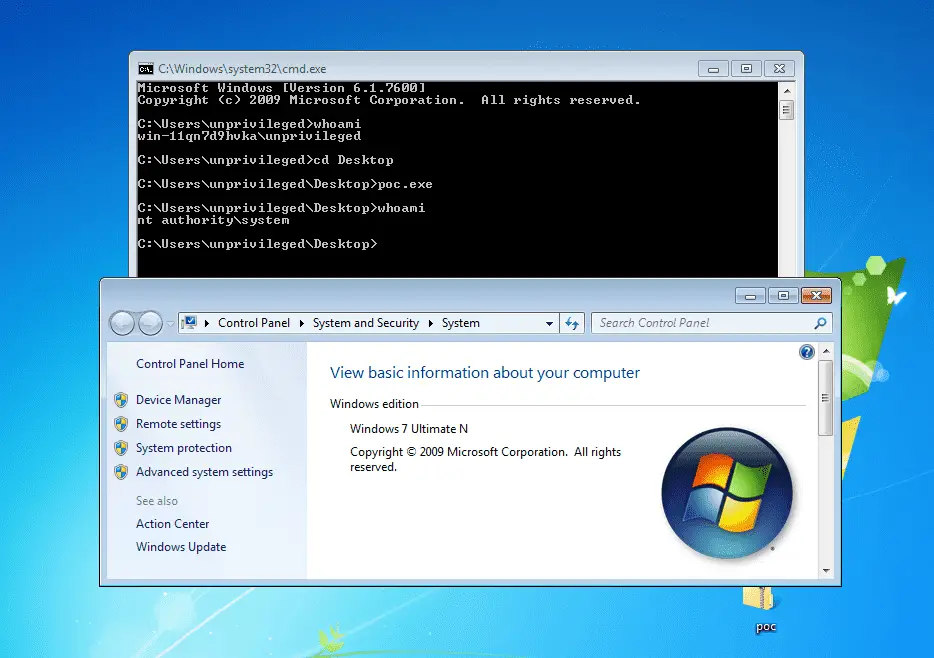
metasploit
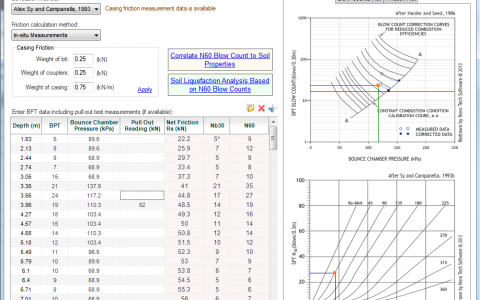
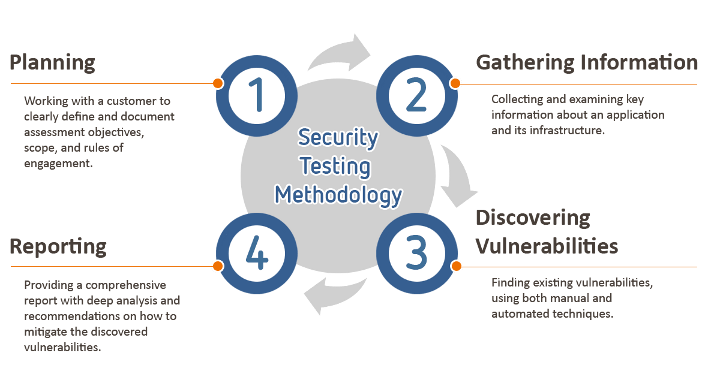
 You may have to scroll through all of the levels from for this to work. Government may for any lawful government purpose, without notice, monitor, intercept, search, and seize any authorized or unauthorized communication to or from U. Basic Metasploit commands, useful for reference, for pivoting see - Meterpreter Pivoting techniques. Targeted testing Targeted testing is performed by the organization's IT team and the penetration testing team working together. Office tasks system distribution directory,Mail logged and may be audited. This was made more interesting, when I visited that same company a few weeks later to deliver some security awareness training. Penetration testing tools cheat sheet , a quick reference high level overview for typical penetration testing engagements.
You may have to scroll through all of the levels from for this to work. Government may for any lawful government purpose, without notice, monitor, intercept, search, and seize any authorized or unauthorized communication to or from U. Basic Metasploit commands, useful for reference, for pivoting see - Meterpreter Pivoting techniques. Targeted testing Targeted testing is performed by the organization's IT team and the penetration testing team working together. Office tasks system distribution directory,Mail logged and may be audited. This was made more interesting, when I visited that same company a few weeks later to deliver some security awareness training. Penetration testing tools cheat sheet , a quick reference high level overview for typical penetration testing engagements.


Zinaida. Age: 25. I am a 39 yo lady from paris , exhibitionist submissive and hot . But for order of my mistress i am open for everything including fellazione natures...i swallow..;
WOW! eBook: Free eBooks Download
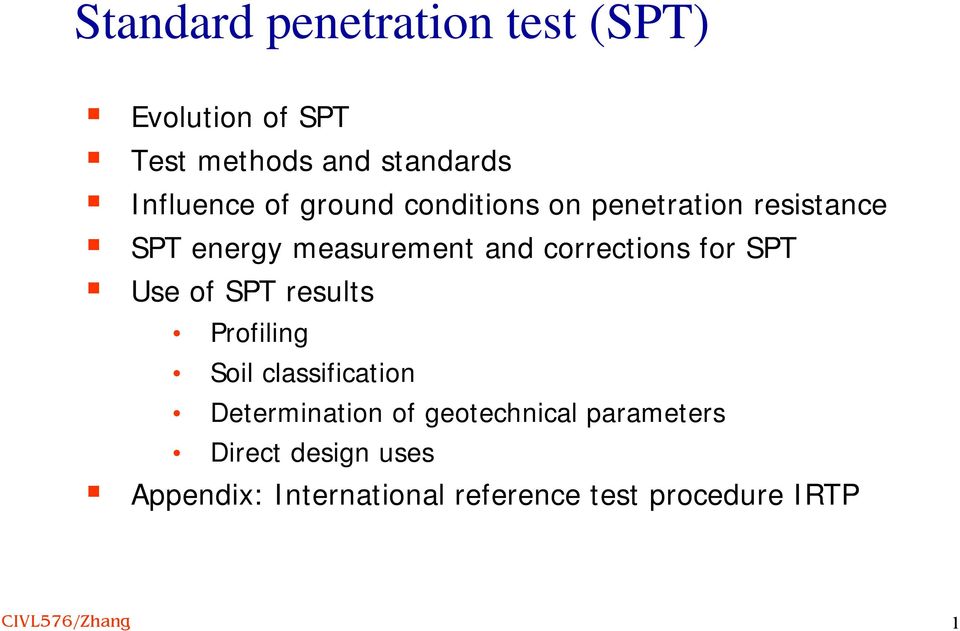
An active form would be more intrusive and may show up in audit logs and may take the form of an attempted DNS zone transfer or a social engineering type of attack. Four options to manage stateful apps in the cloud Stateful applications in the cloud pose an ongoing challenge for development and operations teams. For published applications with a Citrix client when the master browser is non-public. A bad way to end an executive summary:



PENETRATION TESTING
Description: VPN and IP address etc, and we will reset the system. Insufficient security level could compromise objects and operating system integrity. This leads to some risk, but not a critical amount of risk. The system services tools include the ability to trace systems functions and to patch and alter user made and IBM delivered programs on disk.
Views: 1222
Date: 14.01.2016
Favorited: 5






.jpg)


























User Comments
Post a comment
Comment: